|
|
Post by turtle on Jan 14, 2004 15:41:07 GMT 8
|
|
|
|
Post by enigma on Jan 14, 2004 15:45:58 GMT 8
o..ok..home edition...thanx.. |
|
|
|
Post by StRiDeR on Jan 14, 2004 19:21:28 GMT 8
yg paling aku benci bila dah update winxp. pas restart je. pc mula wat hal, hang, startup jadi lombab la, system resources makan byk ram la, skang nie load winxp je dah makan 140mb. aku dah disable smua prog yg x guna pun still makan ram. tah le ape punya bangang programmer microsoft svhost.exe - 2,452k svhost.exe - 8,640k <- 8mb yg x tahan nie svhost.exe - 3,004k kalo ade 1 svhost.exe xperla gak, nie sampai 3. lombab la pc aku nieeee hadoi apasal kau nyer besar sangat?  ..."svhost.exe - 8,640k <- 8mb yg x tahan nie"....aku nyer paling tinggi pun 3,000k jer.... |
|
|
|
Post by turtle on Jan 14, 2004 21:28:38 GMT 8
ermmm lepas 6 jam pc aku jalan. si svchost.exe ni da naik sampai 19,820k. tahler mayb pasal network kot
cuba masok google.com keyword winxp svchost.exe
svchost mmg winxp punya prog x leh la nak kill. kalo svhost leh ler kill
|
|
|
|
Post by atokENSEM on Jan 15, 2004 1:45:23 GMT 8
strider?u 1st batch?
|
|
|
|
Post by StRiDeR on Jan 15, 2004 8:30:26 GMT 8
ermmm lepas 6 jam pc aku jalan. si svchost.exe ni da naik sampai 19,820k. tahler mayb pasal network kot cuba masok google.com keyword winxp svchost.exe svchost mmg winxp punya prog x leh la nak kill. kalo svhost leh ler kill The Svchost.exe file is located in the %SystemRoot%\System32 folder. At startup, Svchost.exe checks the services portion of the registry to construct a list of services that it needs to load. Multiple instances of Svchost.exe can run at the same time. Each Svchost.exe session can contain a grouping of services, so that separate services can run, depending on how and where Svchost.exe is started. This allows for better control and easier debugging. Svchost.exe groups are identified in the following registry key: HKEY_LOCAL_MACHINE\Software\Microsoft\WindowsNT \CurrentVersion\Svchost Each value under this key represents a separate Svchost group and is displayed as a separate instance when you are viewing active processes. Each value is a REG_MULTI_SZ value and contains the services that run under that Svchost group. Each Svchost group can contain one or more service names that are extracted from the following registry key, whose Parameters key contains a ServiceDLL value: HKEY_LOCAL_MACHINE\System\CurrentControlSet \Services\Service To view the list of services that are running in Svchost: Click Start on the Windows taskbar, and then click Run. In the Open box, type CMD, and then press ENTER. Type Tasklist /SVC, and then press ENTER. Tasklist displays a list of active processes. The /SVC switch shows the list of active services in each process. For further information about a process, type the following command, and then press ENTER: Tasklist /FI "PID eq processID" (with the quotation marks) The following example of Tasklist output shows two instances of Svchost.exe that are running. Image Name PID Services ==================================== ==================================== System Process 0 N/A System 8 N/A Smss.exe 132 N/A Csrss.exe 160 N/A Winlogon.exe 180 N/A Services.exe 208 AppMgmt,Browser,Dhcp,Dmserver,Dnscache, Eventlog,LanmanServer,LanmanWorkstation, LmHosts,Messenger,PlugPlay,ProtectedStorage, Seclogon,TrkWks,W32Time,Wmi Lsass.exe 220 Netlogon,PolicyAgent,SamSs Svchost.exe 404 RpcSs Spoolsv.exe 452 Spooler Cisvc.exe 544 Cisvc Svchost.exe 556 EventSystem,Netman,NtmsSvc,RasMan, SENS,TapiSrv Regsvc.exe 580 RemoteRegistry Mstask.exe 596 Schedule Snmp.exe 660 SNMP Winmgmt.exe 728 WinMgmt Explorer.exe 812 N/A Cmd.exe 1300 N/A Tasklist.exe 1144 N/A The registry setting for the two groupings for this example are as follows: HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Svchost: Netsvcs: Reg_Multi_SZ: EventSystem Ias Iprip Irmon Netman Nwsapagent Rasauto Rasman Remoteaccess SENS Sharedaccess Tapisrv Ntmssvc RApcss :Reg_Multi_SZ: RpcSs emm....pasal tue aku x tau lah....tapi berdasarkan description kat atas....aku rasa kau leh limitkan dia punya service....x pun terminate some program yg x guna....cuba kau pergi kat run....pastu taip msconfig....pastu kau buang lah aper yg kau rasa membebankan OS ngan memory kau....tapi berhati2 sblm kau terminate kan sesetengah program tue...takut2 OS kau crash lak.... |
|
|
|
Post by StRiDeR on Jan 15, 2004 8:34:57 GMT 8
|
|
|
|
Post by StRiDeR on Jan 15, 2004 8:51:57 GMT 8
page 6 - Configuring the Windows XP Firewall ---------------------------------------------------------- All firewall methods, with the exception of application level gateways, use ports, protocol types and IP addresses or computer names to control data entering your network. This is the most important thing to understand. Once you get used to the idea of opening or closing ports in order to control what gets in or out of your network, you can easily configure almost any basic firewall product. The firewalls we will deal with here, and most of the commonly available commercial ones will block all ports coming into the firewall by default, so if you wish to allow computers on the internet access to a certain part of your network, you will have to do some configuration. You will also need to research the application and find out what ports it uses. All software manufacturers should offer this information. Now let's look at configuring two of the most common types of firewall; The firewall program included with the Windows XP operating system, and a typical cable/DSL router. Configuring the Windows XP firewall: This is an easy one, so let's start with it. To enable the firewall, go to start/control panel/network and Internet connections/network connections then right click on your Internet connection and select 'properties'  Go to the 'advanced' tab and check the 'internet connection firewall' box.  Hmm, that was tough. If you remember the definitions from above, what you have just done is enabled a combination of packet filtering and a circuit level gateway. Your computer will now record which applications on your computer attempt to access the Internet, and examine all incoming data against these records. Any unsolicited data will be dropped. If you choose to use Internet connection sharing as well, the firewall will handle requests from the other computers in your network as well, acting as a gateway. The XP firewall is effective at stopping unauthorized data from entering your computer or network. lau korang nak senang....x yah download2 firewall...pakai jer firewall yg ader kat window XP nie... |
|
|
|
Post by turtle on Jan 15, 2004 11:51:44 GMT 8
Since the release of Windows XP, there has been a lot of hype about security, and about Windows XP’s built in firewall. Although the built in firewall certainly seems like a good step in the right direction, it can be a double edged sword. In this article, I’ll explain the good points and the bad points of the Windows XP firewall. The Windows XP firewall is designed to block all inbound packets, unless those packets are in a direct response to a query that was sent out from the machine. The firewall is designed to help you keep hackers out of your system. As you can see in Figure A, port scanning a Windows XP machine that doesn’t have the firewall enabled reveals some information that could be useful to a hacker. However, if you enable the firewall and then perform the same port scan a second time, nothing is revealed Figure A Performing a port scan on a machine without the firewall reveals some useful informationFigure B Performing a port scan on a machine without the firewall reveals some useful informationFigure B the firewall prevents port scans the firewall prevents port scansAs you can see in my figures, the firewall protects Windows XP against port scanning. Unfortunately though, there are some serious issues involved in using the Windows XP firewall that you need to be aware of. First, the Windows XP firewall isn’t a full featured firewall. Normal firewalls allow you to specifically control each TCP and UDP port. Windows XP’s firewall doesn’t provide you with this capability. Instead, it takes a point and click approach to enabling or disabling a few common ports, as shown in Figure C. The firewall’s logging capabilities are also minimal. Figure C Windows XP’s firewall allows you to open or close a few common ports. Windows XP’s firewall allows you to open or close a few common ports.Because of the limitations that I’ve just described, the Windows XP firewall shouldn’t be used to take the place of a normal corporate firewall. Instead, it should be used as a supplement. Remember that your corporate firewall does a good job protecting your organization from external threats, but does noting to protect your organization from internal threats. On the other hand, the Windows XP firewall isn’t a suitable replacement for a corporate firewall, but it can help guard workstations from hack attempts originating from within the organization. Therefore, I recommend enabling the Windows XP firewall on your workstations, but using the Windows XP firewall in conjunction with your corporate firewall. Keep in mind though that even the multilevel firewall architecture that I just described isn’t completely secure. The Windows XP firewall does a great job blocking inbound traffic, but makes no attempts to filter outbound traffic. This means that a hacker would have no trouble using your workstations as a part of a distributed denial of service attack. Unfortunately, there’s no way to block outbound traffic at the Windows XP level, but you can configure your corporate firewall in a manner that protects your company against being used as a pawn in a denial of service attack. |
|
|
|
Post by StRiDeR on Jan 15, 2004 12:32:11 GMT 8
memang lah build in firewall xp...byk kekurangan....just cadangan jer...saper yg malas sangat nak download2 firewall nih....tapikan aper yg diciptakan manusia....walaupun hampir perfect, mesti ader kelemahan dia....kerana kita just a human being....
|
|
|
|
Post by turtle on Jan 16, 2004 0:31:17 GMT 8
|
|
|
|
Post by atokENSEM on Jan 18, 2004 4:54:26 GMT 8
erm..2nd batch kot!  |
|
|
|
Post by enigma on Jan 19, 2004 15:47:46 GMT 8
erm..2nd batch kot!  kalau x silap..si strider ni tgh praktikal....atok... |
|
|
|
Post by StRiDeR on Jan 19, 2004 20:24:31 GMT 8
Client Filtering Another option which may be available is client filtering, which is sort of a reverse firewall, blocking clients inside the network from accessing certain ports. All of these methods use essentially the same forms of information: port numbers. Once you get used to the idea of ports as the way applications get information in and out of your computer, configuring these options are simple. Port mapping requires the identification of a machine on your network by name or IP address, a port to be accessed on that machine, and a port to be accessed on your firewall, and the type of protocol (TCP or UDP). 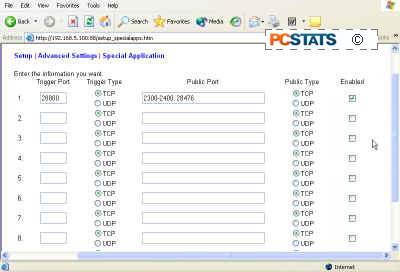 Special application exceptions require a 'trigger port' which sends data out from that application, and one or more receiving ports, depending on the requirements of the application. 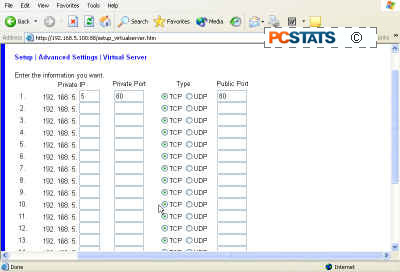 TCP or UDP must also be specified.
|
|
|
|
Post by turtle on Jan 19, 2004 22:58:23 GMT 8
|
|